The Cognitive Campus Center Journey
For decades, the industry had accepted a status quo plagued by fragile, overly complex, disparate operating systems, rigid hardware controllers,...

The Networking industry is undergoing a metamorphosis. Modern networking operations teams are challenged to cope with multiple operational models. As attackers become better and better at breaching our defenses, security analysts are increasingly at the heart of a security organization. The operators are responsible for detecting, investigating and remediating potential breaches before they progress into brand, customer, financial and IP damage. This confluence of DevOps, NetOps, SecOps, and CloudOps demands persistent operations control. How do you cope with decades of security, threat and cyber detection done in reactive silos? What happens as more workloads move to the cloud? At Arista, we value our ecosystem of security partners and networking must adapt to the new complex threats.
Network forensics platforms built on outdated architectures are difficult to adapt to today’s rapidly evolving security attacks. Legacy networks are often unreliable, unmanageable and unscalable, with storage for days and weeks when attackers lurked for months. Networks have become so large, complex and dynamic that understanding who owns what devices, where they are, and if they are doing something malicious, has become insurmountable without new tools.
Security operations teams are like understaffed police and fire departments, mandated to protect neighborhoods without the necessary safety equipment, while only equipped with a flashlight to search every smoke filled house in the dark. These two worlds must deliver an overall environment of secure network visibility in their investigations across client to cloud logs, directories and assets for a more complete picture. Experts don’t have enough time, and organizations don’t have enough experts. A novel paradigm that is a far cry from the traditional approach to security is needed for the decade.
Network Detection & Response – The New Paradigm
Our customers’ CIO/CSOs need a complete and comprehensive network baseline of truth. Simply storing the raw data isn’t enough — as an industry we are already drowning in insufficient and incomprehensible data. A new class of Network Detection and Response (NDR) security is emerging and required. It must consume and provide usable, rich visibility into the environment and analyze it predictively. It complements many of the Endpoint Detection Response (EDR) offerings today such as Crowdstrike, etc. and Security Information and Event Management (SIEM) offerings for log analysis such as Splunk to form the Security Operations Center (SOC) Visibility Triad as shown in the figure below.
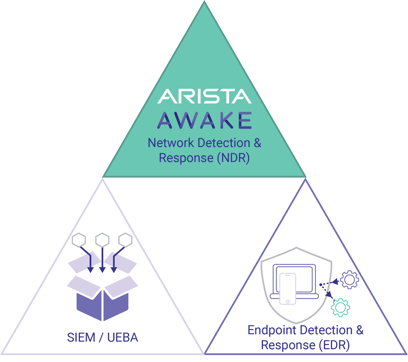
Figure: The SOC Visibility Triad (defined by Gartner in 2019) consists of SIEM vendors for log analysis, EDR vendors for endpoint capture and NDR for analyzing and responding to network-based threats.
While many vendors are marketing their products as network based NDR, the functionally of the products vary by marketing mileage. They are often based on legacy anomaly detection models or proprietary monitoring (such as NetFlow). Of course, these constrained and limiting ways do not gather or protect the information. New and novel NDR architectures, such as Awake Security have recently emerged. Going well beyond mirrored interfaces, Awake’s goal brings customers proactive visibility and threat detection across client to cloud network traffic.
Introducing Awake’s AI-based Security
Arista is pleased to announce the next natural step in our M&A journey with the acquisition of Awake Security. Just as Arista redefined networking with Arista state driven EOS in the 2010 era, we immediately were drawn to the disruptive security and AI-driven model developed by Awake Security for these compelling reasons:
Arista and Awake: Secure Data Driven Networking
It is a difficult and confusing time in security for enterprises. Workloads are moving to cloud. Threats are blurring the perimeter and trust boundaries are spanning from client to campus to cloud. The ability to distinguish data patterns is paramount to building cognitive workspaces and this can only be done with security as a proactive tool not an after-thought. Awake Security and Arista Networks are complementary technologies on several fronts. Arista’s Campus Flow Tracker can work synergistically with Big Switch DMF (DANZ Monitoring Fabric) for monitoring and Awake sensors to augment the threat detection for client to cloud networking. CloudVision and continued integration with our technology partners (Forescout, Okta, Palo Alto, Splunk, VMware, Zscaler) to remediate segmentation policies in cyber security is an ongoing journey.
Looking forward to 2021, I believe networking is at the cusp of an epic transformation in security with proactive detection and response embedded in the network. This new cognitive AI-driven foundation will transform security and campus networking to deliver uniformity across wired, wireless devices, users and the internet of things (IoT). Welcome to the next generation and decade of secure cognitive cloud networking.
It is time for change in security – the time is now!
Reference:

For decades, the industry had accepted a status quo plagued by fragile, overly complex, disparate operating systems, rigid hardware controllers,...
/Images%20(Marketing%20Only)/Blog/Many-Facets-AI-Blog-Image.jpg)
As computational resources scale to meet the demands of large generative artificial intelligence (AI) models, networking plays a crucial role in...
In 2016, Arista Networks together with powerful industry leaders, announced the OSFP (Octal Small Form-Factor Pluggable) specification and...