The Cognitive Campus Center Journey
For decades, the industry had accepted a status quo plagued by fragile, overly complex, disparate operating systems, rigid hardware controllers,...
2 min read
/Images%20(Marketing%20Only)/Blog/Jayshree_Ullal_024.png) Jayshree Ullal
:
Apr 24, 2023 6:00:00 AM
Jayshree Ullal
:
Apr 24, 2023 6:00:00 AM
/Images%20(Marketing%20Only)/Blog/JU-AGNI-Blog.jpg)
The perimeter of networks is changing and collapsing. In a zero trust network, no one and no thing is trusted from inside or outside of the enterprise network without verification or network access control (NAC). However, for years, organizations have been saddled with bolt-on NAC technologies that deliver cost complexity while failing to be effective. Instead, security-conscious organizations are shifting to a “microperimeter” enterprise that embeds security into the network infrastructure as the proactive way to defend today’s wider attack surface.
In the post-pandemic era, we are witnessing edgeless, multi-cloud, multi-device collaboration for hybrid work. However, current NAC solutions are still focused on protecting the attack surface of the last decade and have stagnated, struggling to deliver value quickly and scale with the modern enterprise.
Arista AVA Foundation for Zero Trust
Arista AVA™(Autonomous Virtual Assist) is core to our zero trust networking approach. AVA is built on human and behavioral expertise at cloud scale through an AI-based expert system to automate complex tasks like troubleshooting and defending against cyber threats. AVA is designed for real-time, ground-truth data about the network devices' state and uses an ensemble of AI/ML techniques ranging from supervised and unsupervised machine learning to deep learning and natural language processing (NLP).
The combination of our pervasive network observability, threat detection and response, and segmentation, all powered by AVA, dramatically increases the security and fidelity of the network. Network identity is another critical component for securing the client to campus to cloud enterprise.
Introducing AGNI for Next-Generation Identity
Today Arista is proud to introduce the next frontier of zero trust networking. We are expanding the CloudVision® platform to include AI-driven Arista Guardian for Network IdentityTM (AGNI). Delivered as Software-as-a-Service and powered by AVA, AGNI brings unprecedented simplicity, scale and security to identity management for users and IoT alike. With an API-rich strategy, AGNI can integrate at cloud speed with multiple third-party applications while using the network switch as an identity enabler as shown in the figure below.
/Images%20(Marketing%20Only)/Blog/ZT-v3BlogSlide.png?width=2000&height=920&name=ZT-v3BlogSlide.png)
Novel AI Approach to Network Identity
Applying AVA to identity increases the fidelity, efficacy and coverage for modern network access control. For instance, within AGNI, AVA provides a conversational natural language interface to configure, troubleshoot and analyze NAC policy configurations. It also provides recommendations based on the problem context to simplify day-to-day operations. In the future, AVA will extend these AI-driven capabilities to other parameters, including anomaly detections.
Network Identity as a Service
CV AGNI significantly overcomes legacy NAC to redefine segmentation for the enterprise network that can be applied at any place in the network, depending on the customer's need. Device and user profiles can be used as context in defining traffic segmentation and AGNI greatly simplifies defining these policies together with Arista MSS (macro segmentation service). Drawing on the customer’s existing native cloud-based identity solution for onboarding and securing endpoint devices/users, AGNI simplifies operations and eliminates errors. The CV AGNI platform delivers network identity as a software service across cognitive campus switches and access points, offering cloud-native NAC and management for corporate, BYOD, and IoT devices from any place in the cloud (PIC) location - enterprises, headquarters, branch offices or home office.
The Time is Right for Zero Trust Networking
I am excited to acknowledge and welcome the talented AGNI team of engineers who have reimagined AI-driven network identity. It is the right time to unify the principles of device, identity, network and security for a cognitive and secure client to cloud experience. Security must permeate everything we do on the network and bring that proactive and continuous approach to contextual monitoring and threat hunting all the way from client to multi-cloud. Welcome to the zero trust networking era!

For decades, the industry had accepted a status quo plagued by fragile, overly complex, disparate operating systems, rigid hardware controllers,...
/Images%20(Marketing%20Only)/Blog/Many-Facets-AI-Blog-Image.jpg)
As computational resources scale to meet the demands of large generative artificial intelligence (AI) models, networking plays a crucial role in...
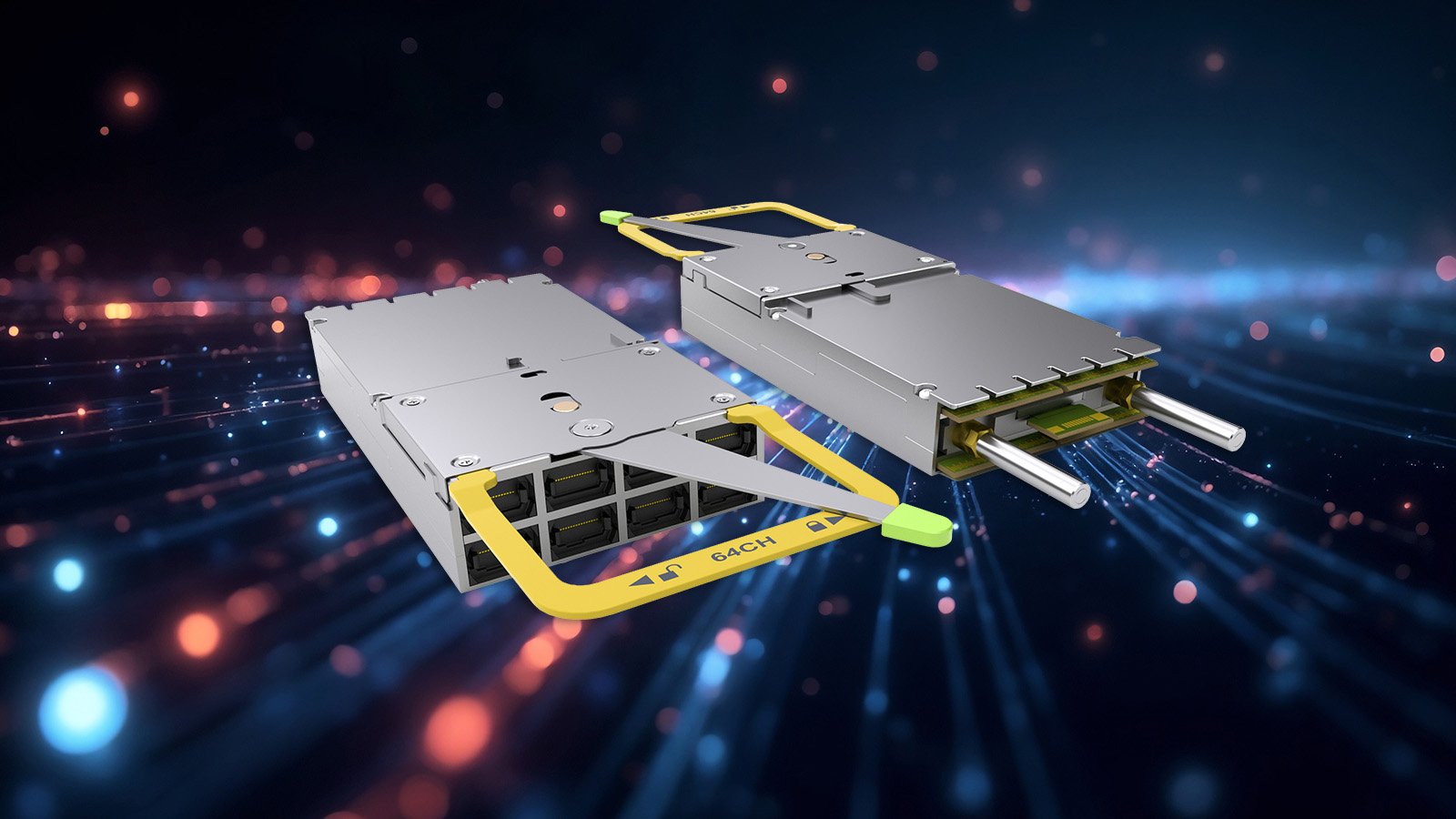
In 2016, Arista Networks together with powerful industry leaders, announced the OSFP (Octal Small Form-Factor Pluggable) specification and...